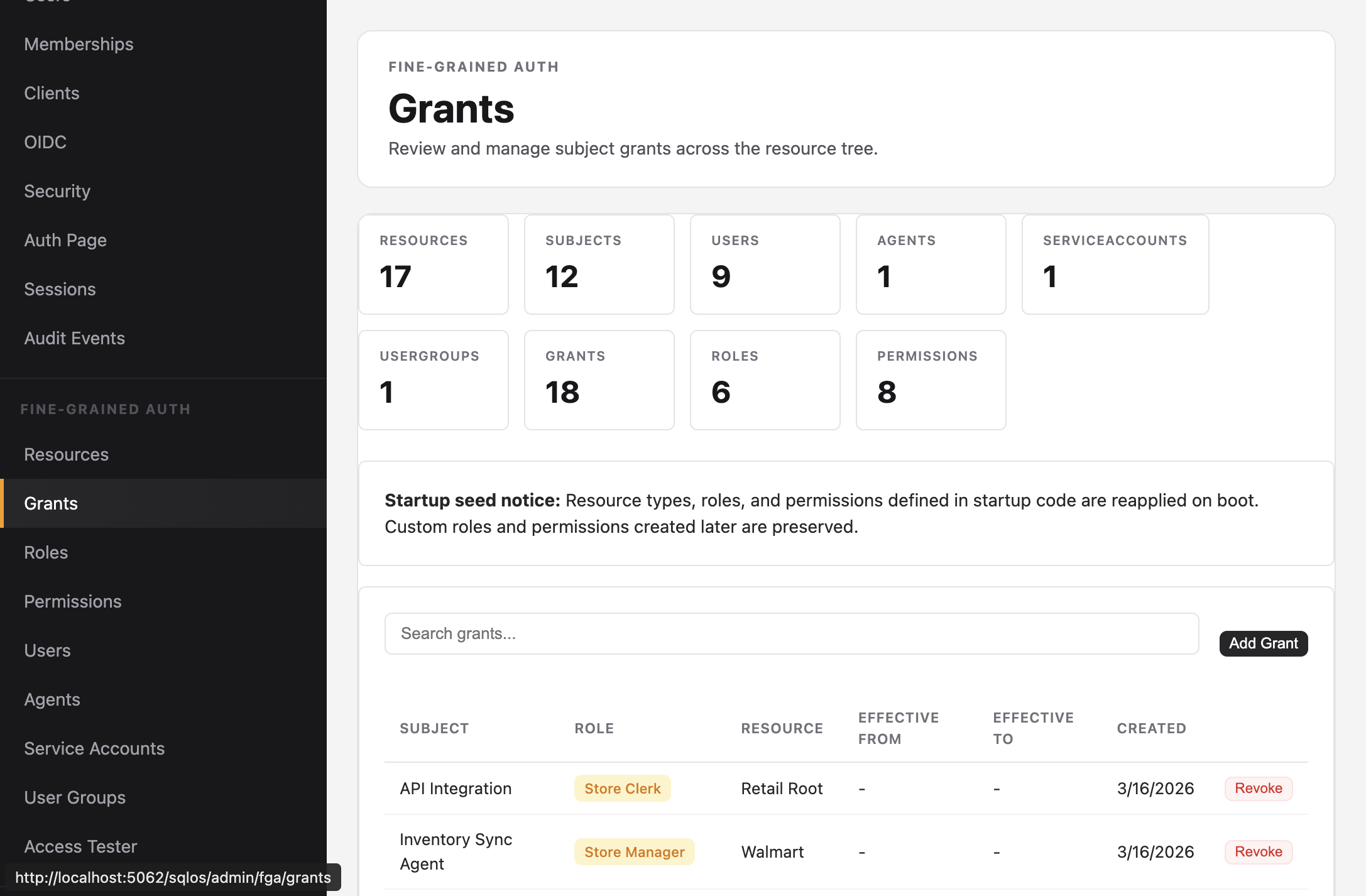
Grants
Assign roles to subjects on resources.
A grant links a subject, a role, and a resource. The subject gains all permissions from the role on that resource and every descendant.
Create a grant
Dashboard: Fine-Grained Auth > Grants
SDK:
context.Set<SqlOSFgaGrant>().Add(new SqlOSFgaGrant
{
Id = SqlOSCryptoService.GenerateId("grant"),
SubjectId = userId,
ResourceId = "org::acme",
RoleId = companyAdminRole.Id,
Description = "Full access to Acme Corp"
});
await context.SaveChangesAsync(ct);
Admin API:
curl -X POST http://localhost:5062/sqlos/admin/fga/api/grants \
-H "Content-Type: application/json" \
-d '{
"subjectId": "usr_...",
"roleId": "role_...",
"resourceId": "org::acme"
}'
Inheritance
Grants inherit downward through the resource tree:
org::acme ← grant: jane / Company Admin
├── walmart ← jane inherits CHAIN_VIEW, CHAIN_EDIT
│ ├── store-001 ← jane inherits LOCATION_VIEW, LOCATION_EDIT
│ └── store-002 ← jane inherits LOCATION_VIEW, LOCATION_EDIT
└── target ← jane inherits CHAIN_VIEW, CHAIN_EDIT
Grant at a higher level = broader access. Grant at a lower level = narrower access.
A Store Clerk granted on store-001 can only see that one store's inventory. A Company Admin granted on org::acme sees everything underneath.
Revoke a grant
Admin API:
curl -X DELETE http://localhost:5062/sqlos/admin/fga/api/grants/{grantId}
Time-bounded grants
Grants support optional EffectiveFrom and EffectiveTo dates for temporary access:
new SqlOSFgaGrant
{
SubjectId = contractorId,
ResourceId = "store-001",
RoleId = storeManagerRole.Id,
EffectiveFrom = DateTime.UtcNow,
EffectiveTo = DateTime.UtcNow.AddMonths(3)
}