Fine-Grained Auth
FGA Overview
Hierarchical authorization for .NET apps with query-time filtering.
FGA models resources as a tree. You grant roles on a node. Child nodes inherit access. EF sends filters to SQL Server. You do not load everything and filter in memory.
How it works#
Define resources (projects, chains, stores), roles (admin, viewer), and permissions (VIEW, EDIT). Grant a role to a user on a resource. Every descendant of that resource inherits the grant.
▾Acme Corp (Organization)
▾Walmart (Chain)
▾Target (Chain)
▾Globex (Organization)
Resources
Organizations, projects, chains, stores, or any hierarchy you define.
Roles and permissions
Attach reusable permission bundles to a resource and inherit them downward.
Query filters
Push auth checks into SQL Server instead of loading data and trimming it in memory.
Query-time filtering#
The core feature. Instead of loading all records and filtering in memory, FGA pushes authorization into the SQL query:
var filter = await authService
.GetAuthorizationFilterAsync<Chain>(subjectId, "CHAIN_VIEW");
var chains = await dbContext.Chains
.Where(filter)
.OrderBy(c => c.Name)
.ToListAsync();Users only see rows they may access. Under the hood that becomes a SQL Server TVF call.
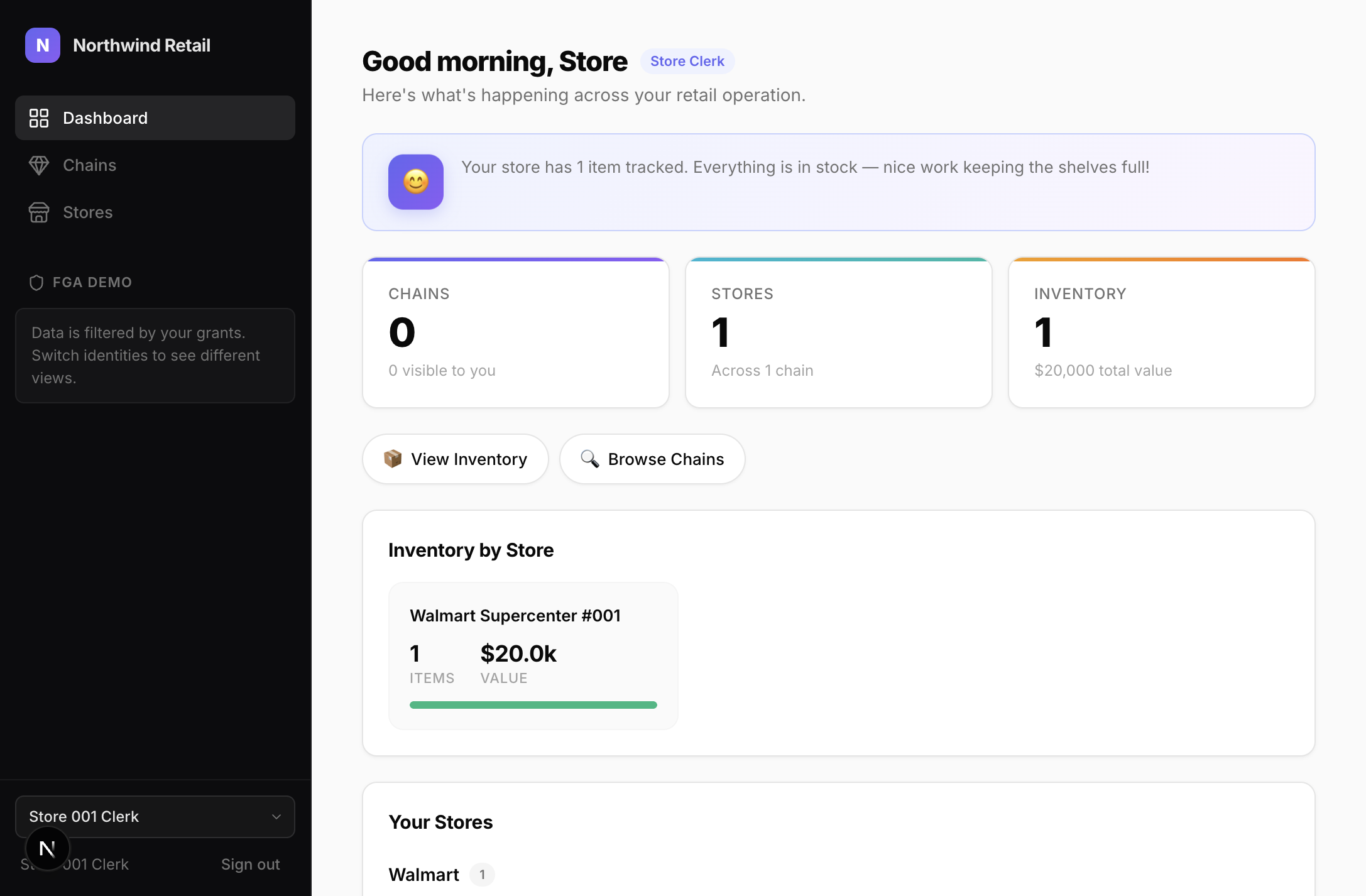
Company Admin sees 5 chains:
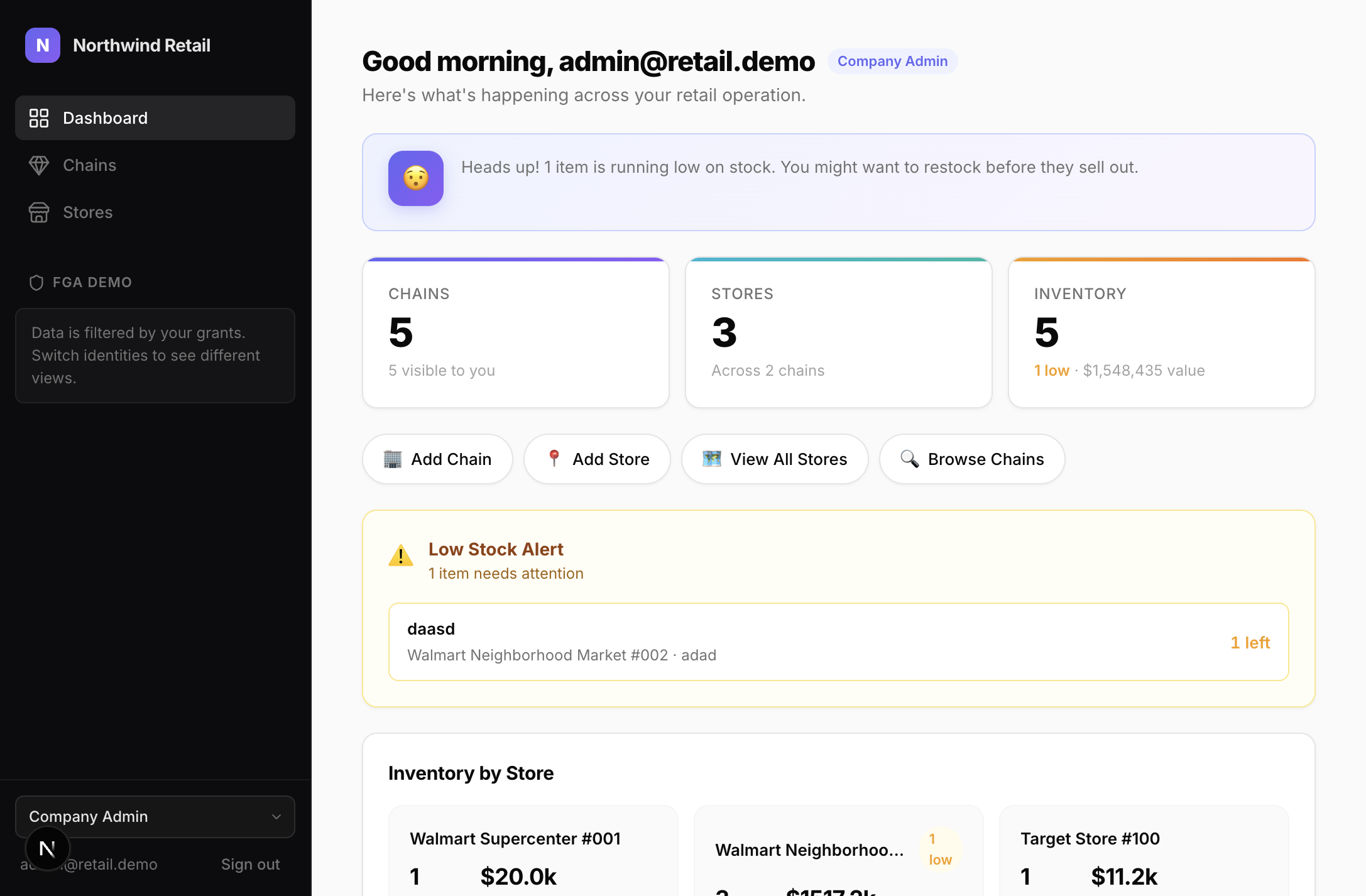
Store Clerk sees 0 chains (only their store):
Setup#
builder.AddSqlOS<AppDbContext>();
var app = builder.Build();
app.MapSqlOS();Dashboard#
/sqlos/admin/fga/ — browse resources, grants, roles, permissions, and run the access tester.
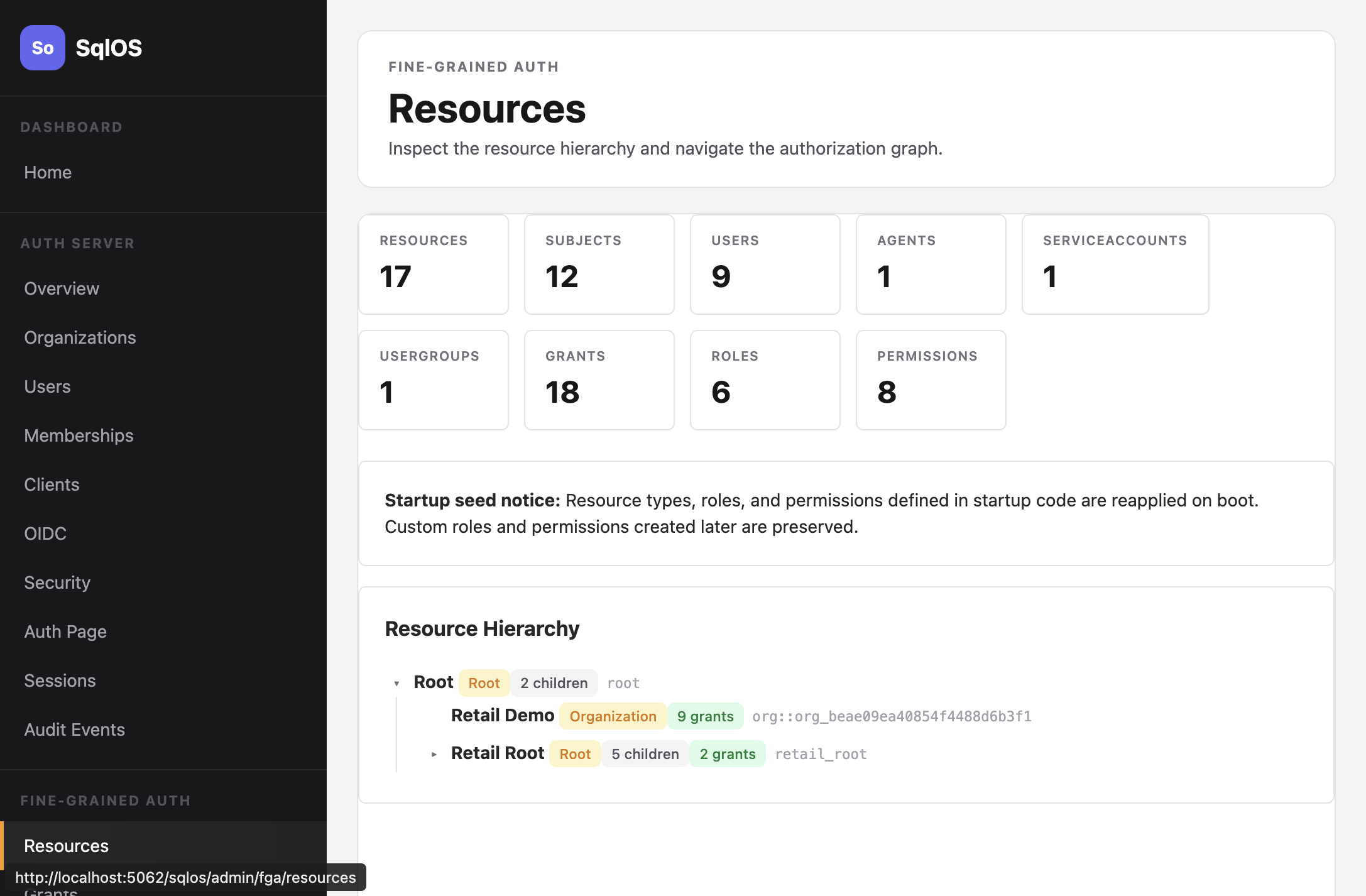
The value proposition is not just expressive permissions. It is that the same authorization model can drive list filtering, detail checks, dashboard inspection, and SQL-native enforcement from one runtime.
Key concepts#
| Concept | Description |
|---|---|
| Resource | A node in the hierarchy (org, project, store) |
| Subject | Who is being authorized (user, agent, service account) |
| Role | A named set of permissions (viewer, editor, admin) |
| Permission | A capability key (CHAIN_VIEW, INVENTORY_EDIT) |
| Grant | Links subject + role + resource; inherits downward |